Cyber attackers look for the easiest way in to your systems: outdated software, unpatched systems, misconfigurations or open ports.
Even a single vulnerability can allow ransomware, data breaches or unauthorised access.
Our vulnerability scanning service continuously checks your systems, cloud environment and devices to uncover weaknesses before they become a threat.
We alert you to risks early, guide you on remediation, and help keep your business protected all year round.

What is Vulnerability Scanning?
Vulnerability Scanning automatically checks your IT environment for security weaknesses that attackers could exploit.
This typically includes:
- Outdated or unpatched software
- Misconfiguration in devices, networks or cloud services
- Weak security settings
- Exposed ports or services
- Unsupported operating systems
- Known vulnerabilities linked to cyber attacks
For businesses, it’s an essential cyber security practice – giving you visibility of risks, helping you prioritise fixes, and supporting Cyber Essentials and Cyber Essentials Plus readiness.
Our scanning service is part of your Unified Security Platform in Elevate and Infinite Assurance, providing continuous visibility as new threats and vulnerabilities emerge.
Vulnerability Scanning Services
Included within our wider Cyber Security offering, our scanning services gives you ongoing insight into your risk posture and ensures that critical weaknesses are identified and addressed quickly by our team.
You’ll get:
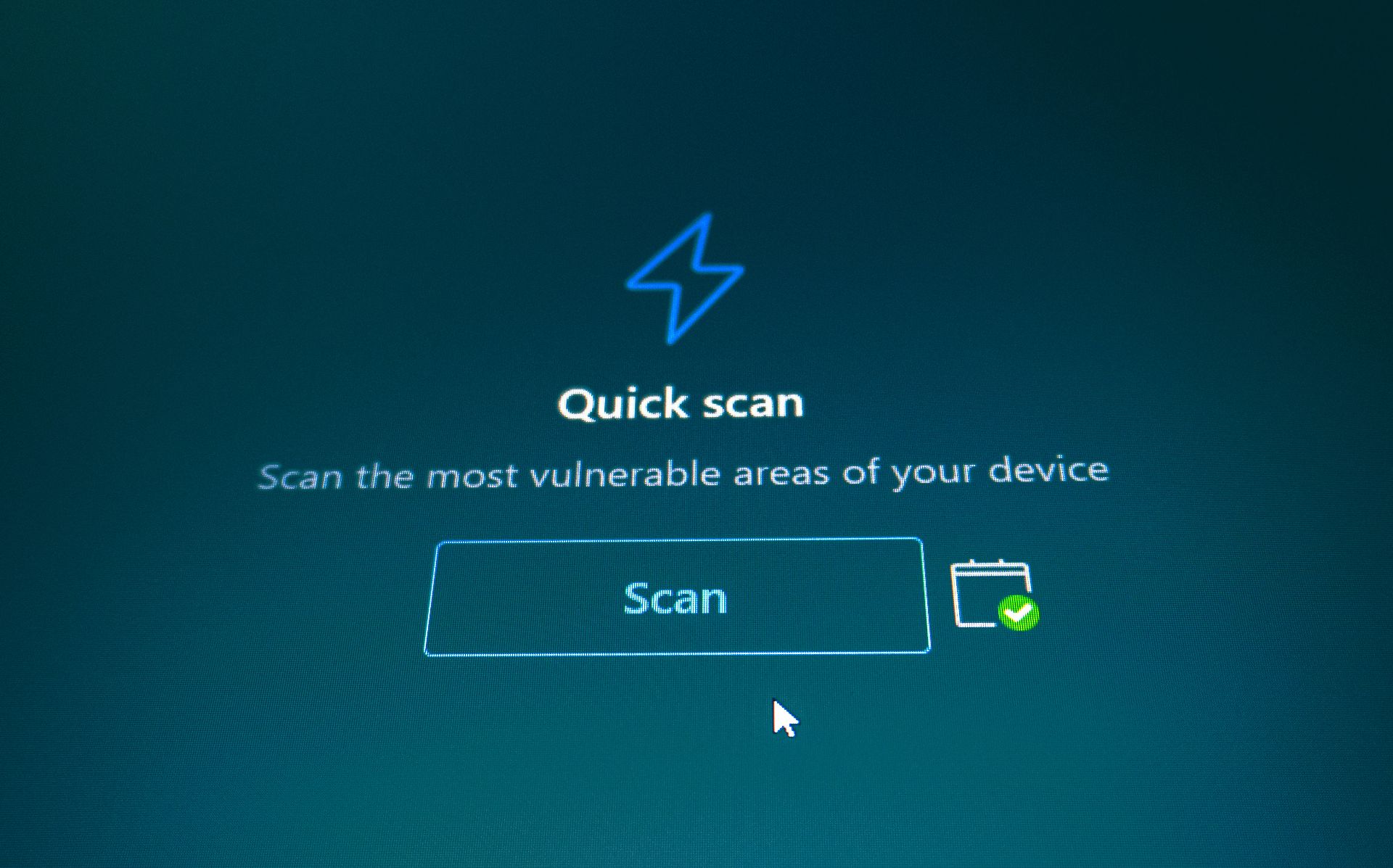
- Automated weekly or monthly vulnerability scans
- Real-time alerts for high-risk vulnerabilities
- Prioritised remediation guidance
- Clear scoring of risk levels
- Monthly vulnerability reports with trend analysis
- Support from your dedicated Customer Success Manager
- Integration with patching, policies and configuration hardening
We handle the scanning, risk identification and guidance – keeping your business one step ahead of threat actors.
Full System Scanning
We scan servers, endpoints, cloud platforms and networks for known vulnerabilities and weaknesses.
Real-Time Alerts
Our team are notified immediately when high-risk vulnerabilities appear – so fixes are prioritised.
Part of Elevate
Fully included within your Unified Security Platform — no additional cost.
Risk Scoring & Reporting
Clear, actionable, insight showing which vulnerabilities matter most and what to do next.
Configuration & Compliance Checks
Identify misconfigurations and security gaps that impact frameworks like Cyber Essentials.
ASM – Third Party Patching
Our team run Advanced Software Management to patch third party applications, not just Microsoft patching.
Ready to strengthen your cyber defences?
Make an enquiry today and we’ll provide a security report showing any immediate vulnerabilities affecting your business.
Frequently asked questions
Why do we need vulnerability scanning?
Because new threats and weaknesses appear everyday – and unpatched systems are one of the most common causes of breaches.
How often do you scan our systems?
Scanning is done continuously, as we monitor your systems daily. You can receive reports weekly or monthly.
What happens when a vulnerability is found?
We will remediate the vulnerability, you will receive the priority score and the next steps in the monthly report from your Customer Success Manager.
Does this integrate with Patching?
Yes – vulnerabilities link directly to patch management with Elevate and Infinite Assurance, making fixes easier and faster.
Does this help with Cyber Essentials?
Yes – regular vulnerability scanning is key to maintaining secure configurations and passing Cyber Essentials or CE+.
Scan For Vulnerabilities
Ensure your business is protected and aware of potential threats to your cyber security and systems
We package Managed IT Services that keep your business running smoothly, at sustainable costs.