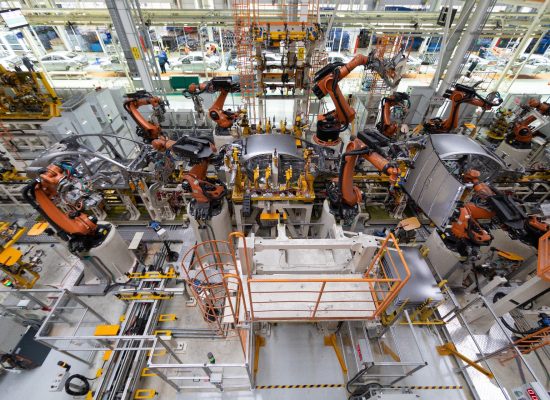
Manufacturing has held the title of the most cyber-attacked industry in the world for four consecutive years – and 2026 shows no signs of slowing down.
Attackers are no longer just stealing data; they are shutting down production, halting logistics, corrupting industrial systems, and targeting OT/IT convergence points.
The latest 2025–2026 threat intelligence paints a worrying picture: manufacturing is now being hit more often, more aggressively, and with higher operational impact than any other sector.
Below is the 2026 state of cyber risk for manufacturers, backed by the newest available industry statistics and recent real-world cases.
Manufacturing Has the Highest Victim Count of Any Industry
Manufacturing remains the most targeted industry according to the 2026 Arctic Wolf Threat & Predictions Report, which found:- The number of victimised manufacturers nearly doubled between 2024 and 2025.
- Manufacturing continues to top IBM’s X-Force list of target sectors for the fourth consecutive year.
Why the increase?
The manufacturing industry is:- Highly reliant on outdated OT systems
- Sensitive to downtime
- Operating huge supply chains
- Holding valuable IP
- Dependent on just-in-time logistics
Ransomware Recovery Costs for Manufacturers Now Average £400,000
According to Arctic Wolf, the median cost of a ransomware attack in manufacturing is now £400,000 – excluding reputational damage, lost contracts, penalties, and recovery labour. Operational downtime is the biggest cost driver. Manufacturers can’t ship, build, or move goods when systems lock. Attackers know this — and exploit it.Real-world Manufacturing Breaches Show the Scale of Disruption
The UK has faced some of the world’s most disruptive manufacturing cyber attacks in recent years. In 2025, Jaguar Land Rover (JLR) was hit by a major ransomware attack that shut down production at its Solihull and Castle Bromwich plants, encrypting critical operational systems and contributing to an estimated £1.9 billion economic impact. Rolls-Royce reported unauthorised access through a third-party supplier, showing how vulnerable even the UK’s most advanced manufacturing ecosystems are to supply-chain compromise. And in one of the UK’s most disruptive food-sector incidents, KP Snacks was forced to halt production across multiple sites after ransomware took down core systems, leading to supermarket shortages nationwide. These incidents underline a clear reality: UK manufacturers are now prime targets for attackers focused not just on data theft, but on shutting down physical operationsPhishing & Social Engineering Are the Primary Entry Point
Manufacturers often assume attackers target firewalls or industrial control systems first. But the data shows something different:- 85% of businesses that suffered cyber incidents experienced phishing as the main cause (UK Cyber Security Breaches Survey 2025).
- Social engineering attacks — supercharged by AI — are now “more convincing and harder to detect” across manufacturing environments.
Supply Chain Attacks Are Soaring: A Major Risk for Manufacturers
Supply chain breaches doubled year-over-year, now making up 15% of all cyber attacks, overtaking stolen credentials as an initial attack vector. Manufacturers are extremely vulnerable because:- They rely on hundreds of suppliers
- Many partners have weaker security
- Attackers use vendor access to infiltrate larger networks
What Manufacturers Should Do in 2026
Given the scale and frequency of attacks, manufacturers should prioritise:- Identity & Access Security
- Mandatory MFA everywhere
- User risk scoring
- Least-privilege access
- Endpoint & Server Protection
- EDR across IT & OT assets where feasible
- Server isolation and segmentation
- Phishing Defence
- Monthly phishing simulations
- Security awareness training
- Impersonation detection
- Supply Chain Risk Management
- Vendor security assessments
- Third-party access monitoring
- Business Continuity
- Offline backups
- Ransomware recovery playbooks
- Incident response rehearsals
- Cyber Essentials / CE+ Certification